
Cybersecurity for embedded systems
Security for Industry 4.0 and IoT - across the complete product lifecycle of embedded systems
The demand for cybersecurity for embedded systems is growing, because the increasing networking of embedded systems in the context of IoT and Industry 4.0 also increases their vulnerability to cyber threats.
Cybersecurity - the security of embedded systems against attacks - is now an important quality feature of networked systems and components.
With comprehensive services and pre-qualified solution modules, NewTec supports component manufacturers, system integrators and operators (OEMs) in mastering the associated challenges:
1. Security by Design: integrate security into the system architecture during development, because subsequent security measures for insecure architectures are expensive, time-consuming and ineffective in the long term.
2. Security over the entire life cycle: ensure that your networked systems are protected at all times, even during operation - through integrated information security and cybersecurity management (ISMS, CSMS) including secure updates against new threats (software update management system, SUMS).
3. Complex, diverting requirements: Reconcile the requirements of security, functionality and above all safety - through a structured, holistic security management process that synchronises all areas of product development (system, security and safety development).
What is Embedded Security?
Embedded security comprises measures to ensure the information security (IT security) of embedded systems. Embedded systems are information-processing systems that are integrated into a larger system and perform certain functions within it (e.g., monitoring, control and regulation, filtering, etc.). Today, such systems are used in a variety of devices and systems, often also in safety-critical application areas such as production environments, medical technology, vehicles or industrial IoT scenarios.
In such embedded systems, special security requirements apply, for example, in terms of availability, tamper resistance, response times (real-time) or the protection of sensitive data. They must be secured against a wide range of possible attack methods, from remote attacks or reading of communications to local manipulation of hardware and supply chain attacks (e.g., on update processes). Complex, often divergent requirements in terms of functionality, cybersecurity and functional safety must be mastered.
Our services in the area of embedded security
In order to implement these complex requirements, NewTec offers a wide range of services and platform solutions for structured security engineering, covering the complete lifecycle of embedded systems. Our offering includes services, pre-qualified hardware and software building blocks, training and consulting on all aspects of embedded security - from system design to secure operation.
Embedded Security: Services and solutions at a glance
Holistic process consulting (NTSecureManagementProcess)
- Structured security management process
- According to IEC 62443-4 and IEC 61508
NewTec Security services
- Consulting: Analyses, concepts, tests and training
- Development support: System Integration/Engineering
- Operational support: Safe operation
Hardware platforms (NTSecureCloudSolutions)
Ready-to-use system modules for secure IoT solutions
- Sensor node: Secure cloud connection
- Secure Gateway: Secure IoT applications
- Cloud-Services: Secure data storage and analysis
Safety with structure: holistic approach
Security services and solutions for the entire lifecycle: Particularly in the case of embedded systems, it is important to ensure effective protection from the initial system design through to decommissioning. That's why our services include risk and requirements analyses, security concepts and tests for robustness and vulnerabilities, as well as support for development and process management and managed services for the continuous protection of your systems during operation. Ready-to-use solution modules reduce your development effort and time-to-market.
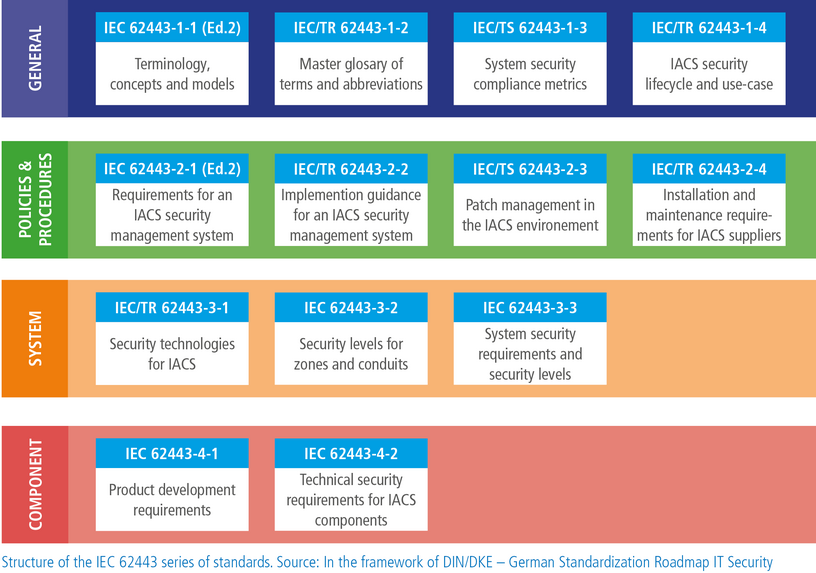
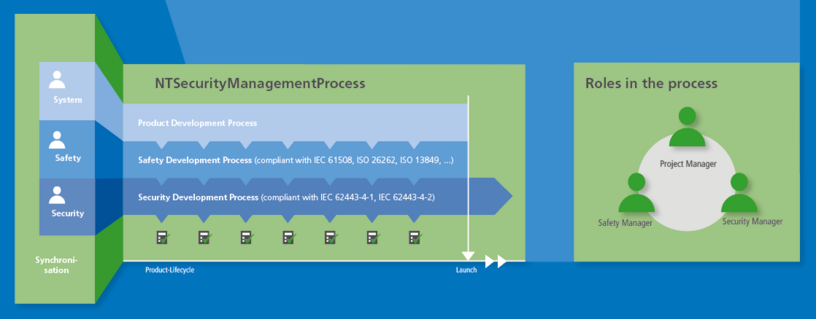
Structured security management process: Disparate requirements must be considered when developing secure networked products. Security requirements can not only affect function and usability, they also interact closely with functional security. Hackers or malware can trigger malfunctions, for example, or security updates can change a system that has been certified as "safe. That is why our holistic security management approach synchronizes all areas of product development (system, security & safety development) according to the specifications of the relevant standards IEC 62443 and IEC 61508 as well as industry-specific cybersecurity standards such as ISO/SAE 21434, UNECE UN R 155 /UN R 156 (automotive) or RTCA DO-326/EUROCAE ED-202 (avionics).
Security Management: Holistic Process Consulting
NewTec's proven security management process - NTSecurityManagementProcess - complements your existing product engineering processes (PEP) with a structured approach to reconcile all requirements from the areas of system development, security and safety and to ensure their implementation. If you wish, we can train and advise your team during the introduction of your security management process or strengthen your project team on site.
Added value for your processes
- Processes compliant with IEC 62443
- Basis for conformity declaration or certification
- Exclusion of liability risks
- Structured controlled process
- Transparency of development steps
- Higher product quality
NewTec Security Services: from concept to operation
NewTec offers a wide range of solutions and services for embedded security engineering, covering the complete lifecycle of your system - from system concept to project implementation and secure operation.
Expert Services to secure your products
System and requirements analyses, security concepts incl. secure update strategies, reviews, penetration & security robustness testing, interim security manager
Engineering and integration support
from system development to security and safety engineering to system integration
Managed services for securing the operation
Tailored operational concepts and managed services including continuous testing for new threats and compliance with security standards as well as incident and obsolescence management for security-related components
Security know-how for your employees: workshops, trainings, seminars
We help you to build up security know-how yourself and to sensitize your employees to information security issues. Learn more about our complete training program.
NTSecureCloudSolutions: System components for secure IoT solutions
Our hardware platforms for embedded systems with end-to-end encryption (NTSecureCloudSolutions) help you bring your secure IoT system to market quickly and without major development effort.
Your benefits
- Highly secure IoT applications with hardware-based end-to-end encryption
- Shorter time-to-market
- Cost savings for development and certification
- Flexibility due to numerous communication interfaces
The NTSecureCloudSolutions include security nodes for cloud connection of sensors and IoT devices (NTSecureNode), a secure IoT gateway (NTSecureGateway), software for trusted communication with cloud services (NTSecureCloudConnector), a highly secure cloud database (NTSecureCloud), and cloud-based data analysis services for various applications.
NTSecureNode BLE100
Data acquisition platform for stationary IoT networks. More...
NTSecureNode NB100
Data acquisition platform for large-area IoT networks (LTE NB-IoT). More...
NTSecureGateway 1000 Family
Easy connectivity for legacy production environments. More...



